Hikvision Senior Director of Cybersecurity: Examples of reCAPTCHAS Hacks and Phishing Threats, Plus 4 Tips to Avoid Becoming a Victim to these Cyberattacks
Hikvision senior director of cybersecurity, Chuck Davis, has been covering numerous recent hacks, cyber threats and attacks in Hikvision’s COVID-19 computer hacks blog series. In today’s blog, he covers phishing websites that are using reCAPTCHA to thwart detection.
The world of cybersecurity is a constant cat and mouse game where attackers find new and creative ways to hack into things and the defenders discover those methods and figure out how to stop the attacks. The latest wrinkle in this spin around the hamster wheel was revealed by researchers at Barracuda Networks, who discovered that threat actors are now using, “reCAPTCHA walls to block URL scanning services from accessing the content of phishing pages.”
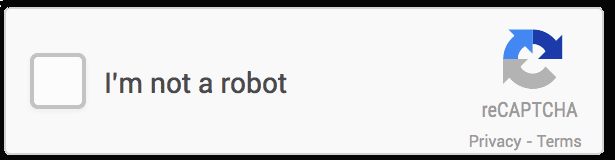
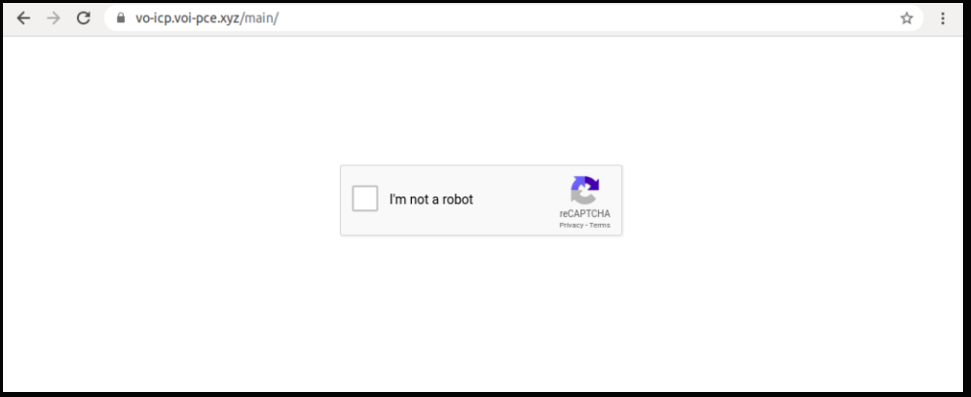
What this means is that if you are tricked into clicking on a link or opening an attachment from a phishing email, you might be met with a real, reCAPTCHA challenge which has you click a check box to prove that you are not a robot. In this context, a “robot” or a “bot” is an automated program that scours the Internet looking to scrape data from sites, create fake accounts or post fake reviews. When you click that box and pass the reCAPTCHA test, you are sent to the malicious phishing page. While clicking that box is an easy test for humans, the automated cybersecurity tools that check the links in our email work much like the malicious bots and are unable to get past that reCAPTCHA to determine if the page has suspicious or malicious content.
What Is CAPTCHA & reCAPTCHA?
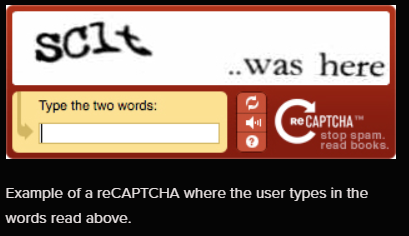
CAPTCHA is an acronym that stands for, Completely Automated Public Turing test to tell Computers and Humans Apart. In 2009, Google acquired a popular version of CAPTCHA technology called the reCAPTCHA. Early versions of reCAPTCHA had website visitors trying to read distorted words, then type them in a box to prove that they are not a robot.
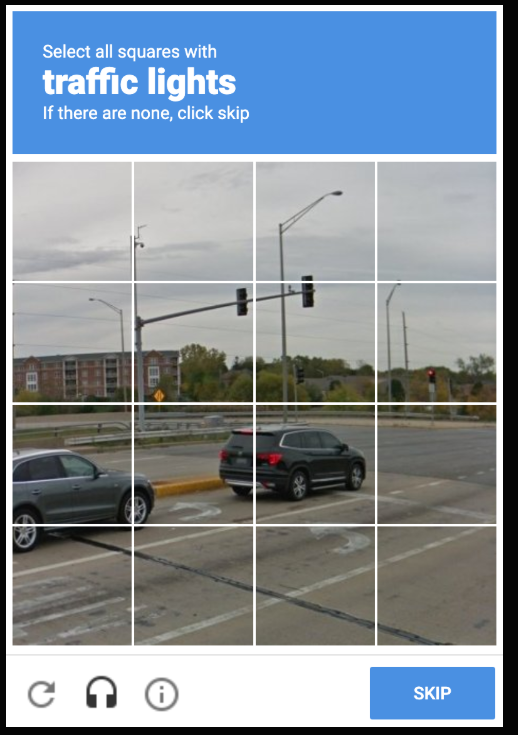
A later version of reCAPTCHA displays an image with grid lines and challenges visitors to solve a simple puzzle like, “Select all squares with traffic lights.” These reCAPTCHA methods are effective but frustrating to users who sometimes fail the tests once or twice before success.
Google’s reCAPTCHA version three was created to relieve the end user of the stress and time needed to pass the previous reCAPTCHAs. In version three, the visitor only needs to check a box to verify that he or she is not a robot. However, the results are similar in that automated bots, both good and bad, are unable to pass the test and see the page behind the CAPTCHA.
The Phish
In the past we have seen phishing pages mimic a reCAPTCHA to make a site look more credible, but now that tactic seems to have been replaced by attackers actually using a reCAPTCHA in most cases. According to Barracuda’s report, “only one email with a fake reCAPTCHA box was detected, compared to more than 100,000 emails using the real API.”
An example from the report shows a phishing page that appears to be an email from Microsoft that is alerting the recipient of a new voicemail.
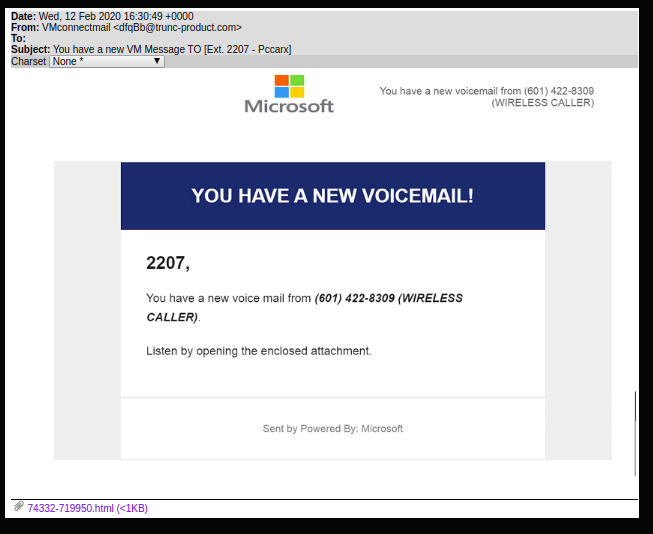
The email contains an attached html file that, when opened, redirects the victim to a reCAPTCHA page.
After the victim solves the reCAPTCHA, they are redirected to the actual phishing page which appears to be a standard Microsoft login page.
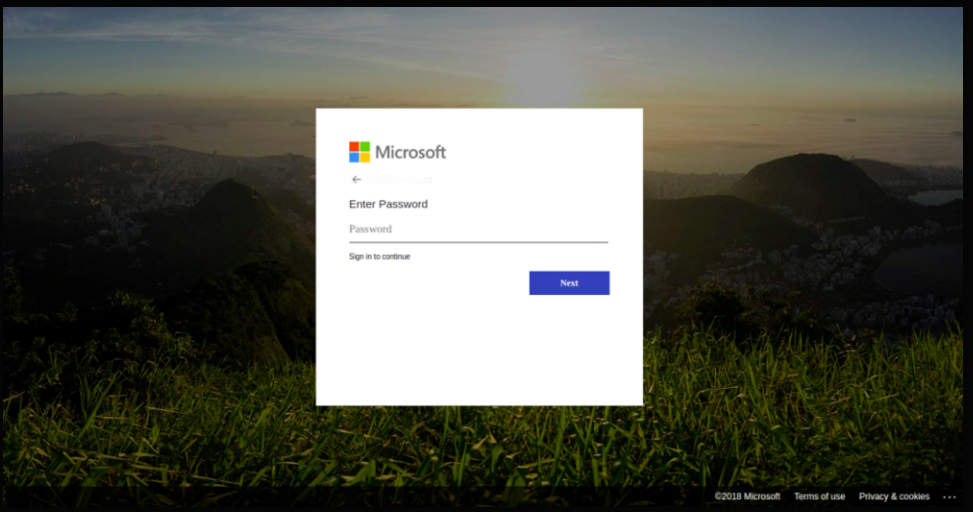
At this point, if the victim falls for the phish, the threat actors now have the victim’s Microsoft username and password.
The use of a real reCAPTCHA is a clever trick to make the victim feel as if the email is valid but it doesn’t just add credibility, it also keeps the automated security, spam and phishing tools from seeing the actual phishing page. Humans are the last line of defense so it’s important to stay alert when checking email because it is one of the few ways that threat actors have to get into our home and work networks.
Four Tips: What Can You Do to Avoid Being a Victim of this Scam?
Below, Hikvision’s Davis offers four tips to prevent becoming a victim of a phishing scam or hack:
- Follow standard phishing detection tips.
- Don’t leave your guard down when you see something that looks credible, like a reCAPTCHA.
- Use a password manager and have it automatically fill in your username and password. If you’re on a phishing site, it won’t paste your credentials into an unrecognized domain, for example microsoft.com versus miicrosoft.com.
- Share this information with friends, family and colleagues because knowledge is power.
